Kaspersky Internet Security 2012
Kaspersky Internet Security 2012
Kaspersky Internet Security 2012
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
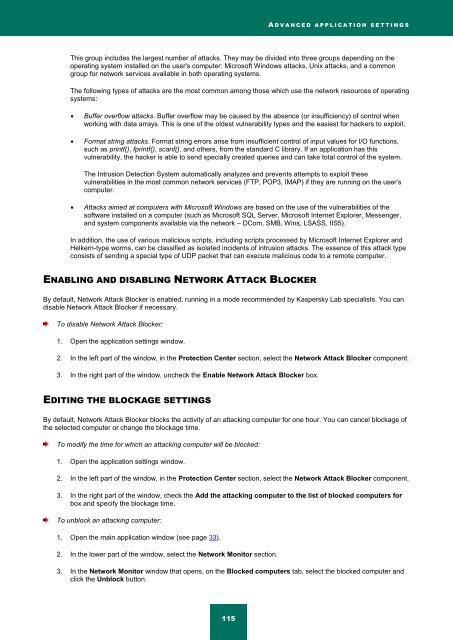
A D V A N C E D A P P L I C A T I O N S E T T I N G S<br />
This group includes the largest number of attacks. They may be divided into three groups depending on the<br />
operating system installed on the user's computer: Microsoft Windows attacks, Unix attacks, and a common<br />
group for network services available in both operating systems.<br />
The following types of attacks are the most common among those which use the network resources of operating<br />
systems:<br />
Buffer overflow attacks. Buffer overflow may be caused by the absence (or insufficiency) of control when<br />
working with data arrays. This is one of the oldest vulnerability types and the easiest for hackers to exploit.<br />
Format string attacks. Format string errors arise from insufficient control of input values for I/O functions,<br />
such as printf(), fprintf(), scanf(), and others, from the standard C library. If an application has this<br />
vulnerability, the hacker is able to send specially created queries and can take total control of the system.<br />
The Intrusion Detection System automatically analyzes and prevents attempts to exploit these<br />
vulnerabilities in the most common network services (FTP, POP3, IMAP) if they are running on the user’s<br />
computer.<br />
Attacks aimed at computers with Microsoft Windows are based on the use of the vulnerabilities of the<br />
software installed on a computer (such as Microsoft SQL Server, Microsoft <strong>Internet</strong> Explorer, Messenger,<br />
and system components available via the network – DCom, SMB, Wins, LSASS, IIS5).<br />
In addition, the use of various malicious scripts, including scripts processed by Microsoft <strong>Internet</strong> Explorer and<br />
Helkern-type worms, can be classified as isolated incidents of intrusion attacks. The essence of this attack type<br />
consists of sending a special type of UDP packet that can execute malicious code to a remote computer.<br />
ENABLING AND DISABLING NETWORK ATTACK BLOCKER<br />
By default, Network Attack Blocker is enabled, running in a mode recommended by <strong>Kaspersky</strong> Lab specialists. You can<br />
disable Network Attack Blocker if necessary.<br />
To disable Network Attack Blocker:<br />
1. Open the application settings window.<br />
2. In the left part of the window, in the Protection Center section, select the Network Attack Blocker component.<br />
3. In the right part of the window, uncheck the Enable Network Attack Blocker box.<br />
EDITING THE BLOCKAGE SETTINGS<br />
By default, Network Attack Blocker blocks the activity of an attacking computer for one hour. You can cancel blockage of<br />
the selected computer or change the blockage time.<br />
To modify the time for which an attacking computer will be blocked:<br />
1. Open the application settings window.<br />
2. In the left part of the window, in the Protection Center section, select the Network Attack Blocker component.<br />
3. In the right part of the window, check the Add the attacking computer to the list of blocked computers for<br />
box and specify the blockage time.<br />
To unblock an attacking computer:<br />
1. Open the main application window (see page 33).<br />
2. In the lower part of the window, select the Network Monitor section.<br />
3. In the Network Monitor window that opens, on the Blocked computers tab, select the blocked computer and<br />
click the Unblock button.<br />
115