Kaspersky Internet Security 2012
Kaspersky Internet Security 2012
Kaspersky Internet Security 2012
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
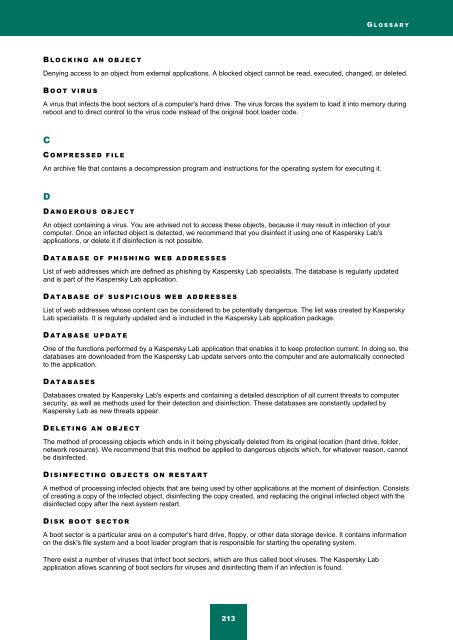
G L O S S A R Y<br />
B L O C K I N G A N O B J E C T<br />
Denying access to an object from external applications. A blocked object cannot be read, executed, changed, or deleted.<br />
B O O T V I R U S<br />
A virus that infects the boot sectors of a computer's hard drive. The virus forces the system to load it into memory during<br />
reboot and to direct control to the virus code instead of the original boot loader code.<br />
C<br />
C O M P R E S S E D F I L E<br />
An archive file that contains a decompression program and instructions for the operating system for executing it.<br />
D<br />
D A N G E R O U S O B J E C T<br />
An object containing a virus. You are advised not to access these objects, because it may result in infection of your<br />
computer. Once an infected object is detected, we recommend that you disinfect it using one of <strong>Kaspersky</strong> Lab's<br />
applications, or delete it if disinfection is not possible.<br />
D A T A B A S E O F P H I S H I N G W E B A D D R E S S E S<br />
List of web addresses which are defined as phishing by <strong>Kaspersky</strong> Lab specialists. The database is regularly updated<br />
and is part of the <strong>Kaspersky</strong> Lab application.<br />
D A T A B A S E O F S U S P I C I O U S W E B A D D R E S S E S<br />
List of web addresses whose content can be considered to be potentially dangerous. The list was created by <strong>Kaspersky</strong><br />
Lab specialists. It is regularly updated and is included in the <strong>Kaspersky</strong> Lab application package.<br />
D A T A B A S E U P D A T E<br />
One of the functions performed by a <strong>Kaspersky</strong> Lab application that enables it to keep protection current. In doing so, the<br />
databases are downloaded from the <strong>Kaspersky</strong> Lab update servers onto the computer and are automatically connected<br />
to the application.<br />
D A T A B A S E S<br />
Databases created by <strong>Kaspersky</strong> Lab's experts and containing a detailed description of all current threats to computer<br />
security, as well as methods used for their detection and disinfection. These databases are constantly updated by<br />
<strong>Kaspersky</strong> Lab as new threats appear.<br />
D E L E T I N G A N O B J E C T<br />
The method of processing objects which ends in it being physically deleted from its original location (hard drive, folder,<br />
network resource). We recommend that this method be applied to dangerous objects which, for whatever reason, cannot<br />
be disinfected.<br />
D I S I N F E C T I N G O B J E C T S O N R E S T A R T<br />
A method of processing infected objects that are being used by other applications at the moment of disinfection. Consists<br />
of creating a copy of the infected object, disinfecting the copy created, and replacing the original infected object with the<br />
disinfected copy after the next system restart.<br />
D I S K B O O T S E C T O R<br />
A boot sector is a particular area on a computer's hard drive, floppy, or other data storage device. It contains information<br />
on the disk's file system and a boot loader program that is responsible for starting the operating system.<br />
There exist a number of viruses that infect boot sectors, which are thus called boot viruses. The <strong>Kaspersky</strong> Lab<br />
application allows scanning of boot sectors for viruses and disinfecting them if an infection is found.<br />
213