Kaspersky Internet Security 2012
Kaspersky Internet Security 2012
Kaspersky Internet Security 2012
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
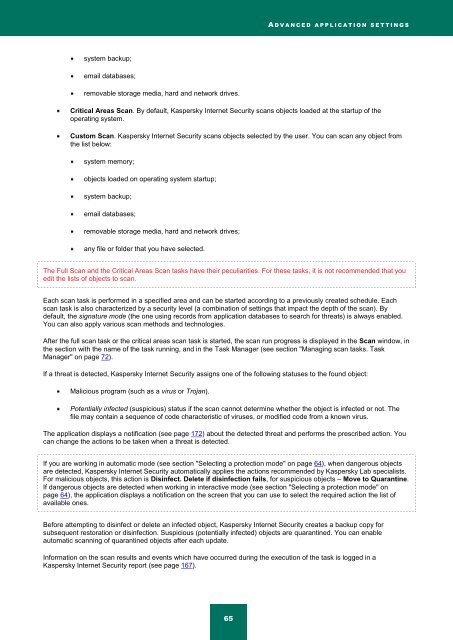
A D V A N C E D A P P L I C A T I O N S E T T I N G S<br />
system backup;<br />
email databases;<br />
removable storage media, hard and network drives.<br />
Critical Areas Scan. By default, <strong>Kaspersky</strong> <strong>Internet</strong> <strong>Security</strong> scans objects loaded at the startup of the<br />
operating system.<br />
Custom Scan. <strong>Kaspersky</strong> <strong>Internet</strong> <strong>Security</strong> scans objects selected by the user. You can scan any object from<br />
the list below:<br />
system memory;<br />
objects loaded on operating system startup;<br />
system backup;<br />
email databases;<br />
removable storage media, hard and network drives;<br />
any file or folder that you have selected.<br />
The Full Scan and the Critical Areas Scan tasks have their peculiarities. For these tasks, it is not recommended that you<br />
edit the lists of objects to scan.<br />
Each scan task is performed in a specified area and can be started according to a previously created schedule. Each<br />
scan task is also characterized by a security level (a combination of settings that impact the depth of the scan). By<br />
default, the signature mode (the one using records from application databases to search for threats) is always enabled.<br />
You can also apply various scan methods and technologies.<br />
After the full scan task or the critical areas scan task is started, the scan run progress is displayed in the Scan window, in<br />
the section with the name of the task running, and in the Task Manager (see section "Managing scan tasks. Task<br />
Manager" on page 72).<br />
If a threat is detected, <strong>Kaspersky</strong> <strong>Internet</strong> <strong>Security</strong> assigns one of the following statuses to the found object:<br />
Malicious program (such as a virus or Trojan).<br />
Potentially infected (suspicious) status if the scan cannot determine whether the object is infected or not. The<br />
file may contain a sequence of code characteristic of viruses, or modified code from a known virus.<br />
The application displays a notification (see page 172) about the detected threat and performs the prescribed action. You<br />
can change the actions to be taken when a threat is detected.<br />
If you are working in automatic mode (see section "Selecting a protection mode" on page 64), when dangerous objects<br />
are detected, <strong>Kaspersky</strong> <strong>Internet</strong> <strong>Security</strong> automatically applies the actions recommended by <strong>Kaspersky</strong> Lab specialists.<br />
For malicious objects, this action is Disinfect. Delete if disinfection fails, for suspicious objects – Move to Quarantine.<br />
If dangerous objects are detected when working in interactive mode (see section "Selecting a protection mode" on<br />
page 64), the application displays a notification on the screen that you can use to select the required action the list of<br />
available ones.<br />
Before attempting to disinfect or delete an infected object, <strong>Kaspersky</strong> <strong>Internet</strong> <strong>Security</strong> creates a backup copy for<br />
subsequent restoration or disinfection. Suspicious (potentially infected) objects are quarantined. You can enable<br />
automatic scanning of quarantined objects after each update.<br />
Information on the scan results and events which have occurred during the execution of the task is logged in a<br />
<strong>Kaspersky</strong> <strong>Internet</strong> <strong>Security</strong> report (see page 167).<br />
65