Kaspersky Internet Security 2012
Kaspersky Internet Security 2012
Kaspersky Internet Security 2012
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
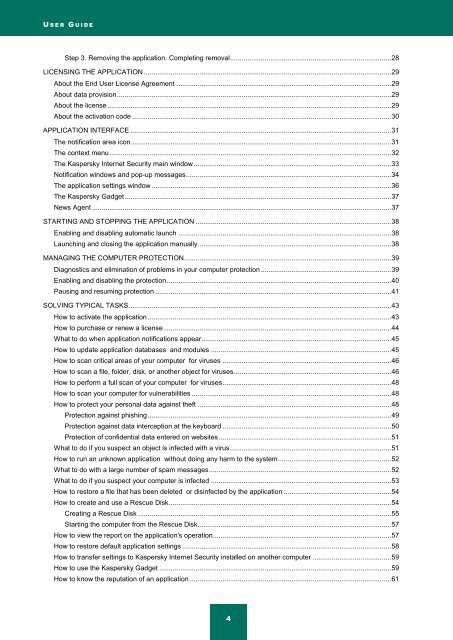
U S E R G U I D E<br />
Step 3. Removing the application. Completing removal .................................................................................... 28<br />
LICENSING THE APPLICATION ................................................................................................................................. 29<br />
About the End User License Agreement ................................................................................................................ 29<br />
About data provision ............................................................................................................................................... 29<br />
About the license .................................................................................................................................................... 29<br />
About the activation code ....................................................................................................................................... 30<br />
APPLICATION INTERFACE ........................................................................................................................................ 31<br />
The notification area icon........................................................................................................................................ 31<br />
The context menu ................................................................................................................................................... 32<br />
The <strong>Kaspersky</strong> <strong>Internet</strong> <strong>Security</strong> main window ....................................................................................................... 33<br />
Notification windows and pop-up messages ........................................................................................................... 34<br />
The application settings window ............................................................................................................................. 36<br />
The <strong>Kaspersky</strong> Gadget ........................................................................................................................................... 37<br />
News Agent ............................................................................................................................................................ 37<br />
STARTING AND STOPPING THE APPLICATION ...................................................................................................... 38<br />
Enabling and disabling automatic launch ............................................................................................................... 38<br />
Launching and closing the application manually ..................................................................................................... 38<br />
MANAGING THE COMPUTER PROTECTION ............................................................................................................ 39<br />
Diagnostics and elimination of problems in your computer protection .................................................................... 39<br />
Enabling and disabling the protection ..................................................................................................................... 40<br />
Pausing and resuming protection ........................................................................................................................... 41<br />
SOLVING TYPICAL TASKS ......................................................................................................................................... 43<br />
How to activate the application ............................................................................................................................... 43<br />
How to purchase or renew a license ....................................................................................................................... 44<br />
What to do when application notifications appear ................................................................................................... 45<br />
How to update application databases and modules .............................................................................................. 45<br />
How to scan critical areas of your computer for viruses ........................................................................................ 46<br />
How to scan a file, folder, disk, or another object for viruses .................................................................................. 46<br />
How to perform a full scan of your computer for viruses ........................................................................................ 48<br />
How to scan your computer for vulnerabilities ........................................................................................................ 48<br />
How to protect your personal data against theft ..................................................................................................... 48<br />
Protection against phishing ............................................................................................................................... 49<br />
Protection against data interception at the keyboard ........................................................................................ 50<br />
Protection of confidential data entered on websites .......................................................................................... 51<br />
What to do if you suspect an object is infected with a virus .................................................................................... 51<br />
How to run an unknown application without doing any harm to the system ........................................................... 52<br />
What to do with a large number of spam messages ............................................................................................... 52<br />
What to do if you suspect your computer is infected .............................................................................................. 53<br />
How to restore a file that has been deleted or disinfected by the application ........................................................ 54<br />
How to create and use a Rescue Disk .................................................................................................................... 54<br />
Creating a Rescue Disk .................................................................................................................................... 55<br />
Starting the computer from the Rescue Disk..................................................................................................... 57<br />
How to view the report on the application's operation ............................................................................................. 57<br />
How to restore default application settings ............................................................................................................. 58<br />
How to transfer settings to <strong>Kaspersky</strong> <strong>Internet</strong> <strong>Security</strong> installed on another computer ......................................... 59<br />
How to use the <strong>Kaspersky</strong> Gadget ......................................................................................................................... 59<br />
How to know the reputation of an application ......................................................................................................... 61<br />
4