Kaspersky Internet Security 2012
Kaspersky Internet Security 2012
Kaspersky Internet Security 2012
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
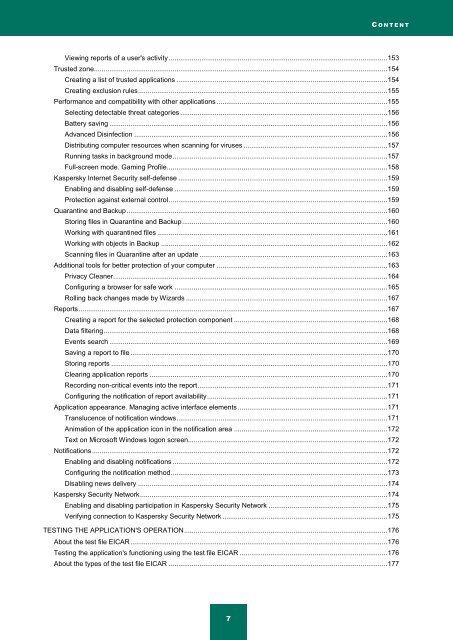
C O N T E N T<br />
Viewing reports of a user's activity .................................................................................................................. 153<br />
Trusted zone ......................................................................................................................................................... 154<br />
Creating a list of trusted applications .............................................................................................................. 154<br />
Creating exclusion rules .................................................................................................................................. 155<br />
Performance and compatibility with other applications ......................................................................................... 155<br />
Selecting detectable threat categories ............................................................................................................ 156<br />
Battery saving ................................................................................................................................................. 156<br />
Advanced Disinfection .................................................................................................................................... 156<br />
Distributing computer resources when scanning for viruses ........................................................................... 157<br />
Running tasks in background mode ................................................................................................................ 157<br />
Full-screen mode. Gaming Profile ................................................................................................................... 158<br />
<strong>Kaspersky</strong> <strong>Internet</strong> <strong>Security</strong> self-defense ............................................................................................................. 159<br />
Enabling and disabling self-defense ............................................................................................................... 159<br />
Protection against external control .................................................................................................................. 159<br />
Quarantine and Backup ........................................................................................................................................ 160<br />
Storing files in Quarantine and Backup ........................................................................................................... 160<br />
Working with quarantined files ........................................................................................................................ 161<br />
Working with objects in Backup ...................................................................................................................... 162<br />
Scanning files in Quarantine after an update .................................................................................................. 163<br />
Additional tools for better protection of your computer ......................................................................................... 163<br />
Privacy Cleaner ............................................................................................................................................... 164<br />
Configuring a browser for safe work ............................................................................................................... 165<br />
Rolling back changes made by Wizards ......................................................................................................... 167<br />
Reports ................................................................................................................................................................. 167<br />
Creating a report for the selected protection component ................................................................................ 168<br />
Data filtering .................................................................................................................................................... 168<br />
Events search ................................................................................................................................................. 169<br />
Saving a report to file ...................................................................................................................................... 170<br />
Storing reports ................................................................................................................................................ 170<br />
Clearing application reports ............................................................................................................................ 170<br />
Recording non-critical events into the report ................................................................................................... 171<br />
Configuring the notification of report availability .............................................................................................. 171<br />
Application appearance. Managing active interface elements .............................................................................. 171<br />
Translucence of notification windows .............................................................................................................. 171<br />
Animation of the application icon in the notification area ................................................................................ 172<br />
Text on Microsoft Windows logon screen........................................................................................................ 172<br />
Notifications .......................................................................................................................................................... 172<br />
Enabling and disabling notifications ................................................................................................................ 172<br />
Configuring the notification method ................................................................................................................. 173<br />
Disabling news delivery .................................................................................................................................. 174<br />
<strong>Kaspersky</strong> <strong>Security</strong> Network ................................................................................................................................. 174<br />
Enabling and disabling participation in <strong>Kaspersky</strong> <strong>Security</strong> Network .............................................................. 175<br />
Verifying connection to <strong>Kaspersky</strong> <strong>Security</strong> Network ...................................................................................... 175<br />
TESTING THE APPLICATION'S OPERATION .......................................................................................................... 176<br />
About the test file EICAR ...................................................................................................................................... 176<br />
Testing the application's functioning using the test file EICAR ............................................................................. 176<br />
About the types of the test file EICAR .................................................................................................................. 177<br />
7