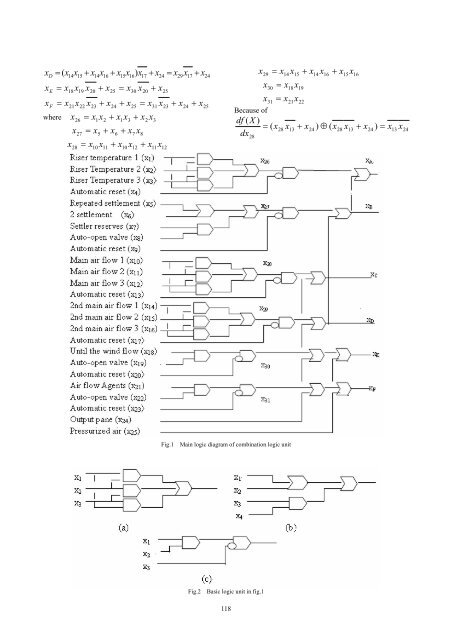
x D = ( x x + x = x x + x 14 x15 + x14x16 + x15x16) x E = x + 17 24 18x19 x20 + x25 = x30 x20 x25 x F = x + 21x22 x23 + x24 + x25 = x31 x23 + x24 x25 x 26 = x1x2 + x1x3 + x2x x 27 = x5 + x6 + x7 x8 x 28 = x10 x11 + x10 x12 + x11x12 where 3 29 17 24 Because of df ( X ) = ( x dx 28 x = + + 29 x14 x15 x14 x16 x15x16 x 30 = x18x19 x 31 = x21x22 28 x 13 + x 24 ) ⊕ ( x 28 x 13 + x 24 ) = x 13 x 24 Fig.1 Main logic diagram of combination logic unit Fig.2 Basic logic unit in fig.1 118
Tabal.1 Combinational fault logic test code of FCC unit Fig x 1 x 2 x 3 x 4 Fig.2(a) s-a-0 fault {0,1,0},{0,0,0},{0,0,1} {1,0,0},{0,0,1},{0,0,0} {1,0,0},{0,1,0},{0,0,0} s-a-1 fault {1,1,0},{1,0,0},{1,0,1} {1,1,0},{0,1,1},{0,1,0} {1,0,1},{0,1,1},{0,0,1} Fig.2(b) s-a-0 fault {0,0,0,1},{0,0,1,0},{0,0,0,0} {0,0,0,1},{0,0,1,0},{0,0,0,0} {0,0,0,1} {0,0,1,0} s-a-1 fault {1,0,0,1},{1,0,1,0},{1,0,0,0} {0,1,0,1},{0,1,1,0},{0,1,0,0} {0,0,1,1} {0,0,1,1} Fig.2(c) s-a-0 fault {0,1,0} {1,0,0} {0,1,0},{0,0,0}{1,0,0},{1,1,0} s-a-1 fault {1,1,0} {1,1,0} {0,1,1},{0,0,1},{1,0,1},{1,1,1} then df ( X ) x 28 = ( x10 x11 + x10 x12 + x11x12 ) x13 x14 dx28 df ( X) x 28 = ( x10 + x11)( x10 + x12)( x11 + x12) x13 x14 dx28 Similarly, we have df ( X ) x 29 = ( x14 x15 + x14 x16 + x15x16 ) x17 x24 dx29 df ( X) x 29 = ( x14 + x15)( x14 + x16)( x15 + x16) x17 x24 dx29 df ( X ) x 30 = x30 x20 x25 dx30 df ( X ) x 30 = x30 x20 x25 dx30 df ( X ) x 31 = x31 x23 x24 x25 dx31 df ( X ) x 31 = x31 x23 x24 x25 dx31 So that the combinational fault test codes of DDS may be computede which are not listed in this paper becaose of too numerous. IV. CONCLUSION (1) The method of fault test codes for identification DDS failures are proposed and be applied in an examples; (2) The results indicate that a) According to the property of the Boolean difference, the codes are available to fined DDS failures; b) In order to identification of DDS failure it is necessary to properly design the combinational logic unit for ensure it has the fault test codes; c) If the DDS failure that had been judged to be identification, the fault test codes should always be used in input of DDS timely to implement self fault test so that its failure may be able to find. Through such means the DDS functions of monitor the production status, prevent and control the potential risk should be achieved correctly. REFERENCES [1] Wang Kaiquan, On the Model of Petrochemical Process Safety Control[J]. Journal of Jiangsu Institute of Petrochemical Technology, Vo1. 11 No.4 Dec. 1999:20-22 [2] Tang Yonghong, system reliability, fault tolerance cut off, and [M]. Chongqing: Chongqing University Press, 1990 edition; 58-79 [3] Yang Yinzhe, the application of intelligent control and research [J]. Scence and Technology Innovation Herald, Vo1. 9 No.22. Nov. 2008:38-42 [4] Gu Li-ping, the use of reliability technology [M]. Beijing: Mechanical Industry Press, .1992 first edition :55-69 [5] Yang Junhua, Fault Diagnosis of the Digital Logic Circuit Bast on Boolean Difference Calculus[J], Journal of University of Electronic Science and Technology of China, Vo1. 14 No.4 Dec. 2005:44-47 [6] Wang kaiquan,. Selection of Assessment Method for Safety Monitoring System[J]. Industrial Safety and Environmental Protection, Vo1. 29 No.1.Jan.2003:230-25 [7] Wang kaiquan,. Study on the Safety system Reliability[J]. Journal of Shanghai Maritirne University, Vo1. 22 No.3 Sep. 2001:169-172 [8] Thannamani G, Narendran TT. Assessment of availabilily of' a fluid catalytic craking uint through simulation[J]. Relialbility Engineering and System Safety, Vo1.20 No.47.1995: 207-220 [9] Wang kaiquan, The Analysis of the Redundant Safety System Reliability[J] Journal of Petrochemical University, Vol.16 No.1 Mar. 2003:64-67 [10] Wang kaiquan, Petrochemical Process Safety and Availability Analyses[J]. Journal of Petrochemical University, Vol.11 No.3. Sep. Mar. 1998:52-54 119
- Page 1 and 2:
Proceedings The Second Internationa
- Page 3 and 4:
Table of Contents Message from the
- Page 5 and 6:
Zuming Xiao, Zhan Guo, Bin Tan, and
- Page 7 and 8:
Message from the Symposium Chairs T
- Page 9 and 10:
Second International Symposium on N
- Page 11 and 12:
ISBN 978-952-5726-09-1 (Print) Proc
- Page 13 and 14:
model that can deal with time serie
- Page 15 and 16:
ISBN 978-952-5726-09-1 (Print) Proc
- Page 17 and 18:
training for the Wushu competition
- Page 19 and 20:
ISBN 978-952-5726-09-1 (Print) Proc
- Page 21 and 22:
information, called weak uncertain
- Page 23 and 24:
Student side Student side Student s
- Page 25 and 26:
ISBN 978-952-5726-09-1 (Print) Proc
- Page 27 and 28:
If we define element of student as
- Page 29 and 30:
ISBN 978-952-5726-09-1 (Print) Proc
- Page 31 and 32:
QoS, each frame data is divided int
- Page 33 and 34:
ISBN 978-952-5726-09-1 (Print) Proc
- Page 35 and 36:
for Imaging Two and Three Phase Flo
- Page 37 and 38:
ISBN 978-952-5726-09-1 (Print) Proc
- Page 39 and 40:
A. Profiling&following control algo
- Page 41 and 42:
Research and Realization about Conv
- Page 43 and 44:
PDF document structure is a tree st
- Page 45 and 46:
ISBN 978-952-5726-09-1 (Print) Proc
- Page 47 and 48:
support 10 Mb / s. But ENC28J60 onl
- Page 49 and 50:
ISBN 978-952-5726-09-1 (Print) Proc
- Page 51 and 52:
condition the first byte output of
- Page 53 and 54:
ISBN 978-952-5726-09-1 (Print) Proc
- Page 55 and 56:
According to maximum membership deg
- Page 57 and 58:
ISBN 978-952-5726-09-1 (Print) Proc
- Page 59 and 60:
ubber according to the mass ratio o
- Page 61 and 62:
Ⅲ. AN IMPROVED DNA ALGORITHM FOR
- Page 63 and 64:
Ⅴ.CONCLUSION REMARKS DNA computer
- Page 65 and 66:
its first child q 1 on the left, th
- Page 67 and 68:
chains can greatly improve efficien
- Page 69 and 70:
II. RELATED WORK A. Mobile Service
- Page 71 and 72:
special services. SOAP is used to b
- Page 73 and 74:
detection methods of DDoS attacks m
- Page 75 and 76:
Step4 calculate the new subordinate
- Page 77 and 78: Figure 1. An analysis of the partit
- Page 79 and 80: ISBN 978-952-5726-09-1 (Print) Proc
- Page 81 and 82: The preceding three formulas can be
- Page 83 and 84: ISBN 978-952-5726-09-1 (Print) Proc
- Page 85 and 86: And the decay speed of buffer seque
- Page 87 and 88: ISBN 978-952-5726-09-1 (Print) Proc
- Page 89 and 90: distance of view point. Given that
- Page 91 and 92: ISBN 978-952-5726-09-1 (Print) Proc
- Page 93 and 94: Ⅳ. EVALUATION OF BLENDED LEARNING
- Page 95 and 96: ISBN 978-952-5726-09-1 (Print) Proc
- Page 97 and 98: symmetric with respect to the origi
- Page 99 and 100: ISBN 978-952-5726-09-1 (Print) Proc
- Page 101 and 102: each sample belongs to each categor
- Page 103 and 104: ISBN 978-952-5726-09-1 (Print) Proc
- Page 105 and 106: A. Data Preparing To generate our t
- Page 107 and 108: ISBN 978-952-5726-09-1 (Print) Proc
- Page 109 and 110: oth α and β . determination of Qu
- Page 111 and 112: ISBN 978-952-5726-09-1 (Print) Proc
- Page 113 and 114: Strong earthquake 0.1< M L
- Page 115 and 116: ISBN 978-952-5726-09-1 (Print) Proc
- Page 117 and 118: indirect causes, and the logical re
- Page 119 and 120: egression. Granger causality test i
- Page 121 and 122: B. Evaluation We have evaluated thi
- Page 123 and 124: used as a source and neighboring ce
- Page 125 and 126: Figure 3. Drainage networks generat
- Page 127: Combinational logic unit failures i
- Page 131 and 132: under the endorsement of both the m
- Page 133 and 134: TABLE I. DESCRIPTION OF PROPOSITION
- Page 135 and 136: Figure 2. The process of the invers
- Page 137 and 138: Figure 9. (a)the original image.(b)
- Page 139 and 140: ISBN 978-952-5726-09-1 (Print) Proc
- Page 141 and 142: In order to reduce to the number of
- Page 143 and 144: ISBN 978-952-5726-09-1 (Print) Proc
- Page 145 and 146: that studying being going to be to
- Page 147 and 148: Reference[10] analyzed the evolutio
- Page 149 and 150: module, communication module, apper
- Page 151 and 152: After the comprehensive performance
- Page 153 and 154: system testing can be seen that the
- Page 155 and 156: III. AUTONOMIC RESOURCE ALLOCATION
- Page 157 and 158: The QoE i (T i ) is the ith user’
- Page 159 and 160: ISBN 978-952-5726-09-1 (Print) Proc
- Page 161 and 162: nodes will be formed one cluster, t
- Page 163 and 164: ISBN 978-952-5726-09-1 (Print) Proc
- Page 165 and 166: Where n is the number of data point
- Page 167 and 168: ISBN 978-952-5726-09-1 (Print) Proc
- Page 169 and 170: Keyboard event Application User mod
- Page 171 and 172: ISBN 978-952-5726-09-1 (Print) Proc
- Page 173 and 174: SQL Azure will eventually include a
- Page 175 and 176: ISBN 978-952-5726-09-1 (Print) Proc
- Page 177 and 178: The nodes in the suffix tree are dr
- Page 179 and 180:
[3] Y. Li, S. M. Chung, and J. D. H
- Page 181 and 182:
some drilling fluid produces hydrog
- Page 183 and 184:
"normalization", whose membership b
- Page 185 and 186:
and minimum structural elements in
- Page 187 and 188:
esults of the spatial transform par
- Page 189 and 190:
B. Research on protocol actions Com
- Page 191 and 192:
ACKNOWLEDGMENT This work is funded
- Page 193 and 194:
A. Problem Description In a small b
- Page 195 and 196:
[4] Huang, Hung, and J. Y. jen Hsu.
- Page 197 and 198:
Further by calculating, the followi
- Page 199 and 200:
TABLE II. THE CONCENTRATION BETWEEN
- Page 201 and 202:
private key that obtained by using
- Page 203 and 204:
ISBN 978-952-5726-09-1 (Print) Proc
- Page 205 and 206:
ontology, and the domain dictionary
- Page 207 and 208:
ISBN 978-952-5726-09-1 (Print) Proc
- Page 209 and 210:
Eq.4 is NP-hard and can be solved b
- Page 211 and 212:
ISBN 978-952-5726-09-1 (Print) Proc
- Page 213 and 214:
Where: G i is the selection field o
- Page 215 and 216:
If there is X j in a generation, wh
- Page 217 and 218:
Theorem 2.4([10]). Let L 1 and L 2
- Page 219 and 220:
The relation between the lattice im
- Page 221 and 222:
Figure 2. Example of single-step de
- Page 223 and 224:
evocation and the fourth group stor
- Page 225 and 226:
focused mainly on rule-based forms
- Page 227 and 228:
Ⅵ. CONCLUSION Figure 6. The Flask
- Page 229 and 230:
EDCF in comparison with DCF, has so
- Page 231 and 232:
B. Simulation results and analysis
- Page 233 and 234:
ISBN 978-952-5726-09-1 (Print) Proc
- Page 235 and 236:
in routing table. When search resou
- Page 237 and 238:
ISBN 978-952-5726-09-1 (Print) Proc
- Page 239 and 240:
others through the selective emotio
- Page 241 and 242:
such as weather information, techno
- Page 243 and 244:
the opening window, a related page
- Page 245 and 246:
1) Process context storage areas. I
- Page 247 and 248:
V. CONCLUSION In this thesis, sCPU-
- Page 249 and 250:
main types of horizontal search env
- Page 251 and 252:
Enterprise Portal security provides
- Page 253 and 254:
() t = [ S () t S () t ] T N S ,...
- Page 255 and 256:
[2] Kumaravel, N., and Kavitha, V.,
- Page 257 and 258:
output, so BP network has been wide
- Page 259 and 260:
input to the artificial neural netw
- Page 261 and 262:
(2) In a process (tokens from outsi
- Page 263 and 264:
The reduction process consists of t
- Page 265 and 266:
all eight normal vectors are identi
- Page 267 and 268:
is B object , and the number of emp
- Page 269 and 270:
xi, j y' = εα ( (1 + tanh( )) −
- Page 271 and 272:
Error 8000 7000 6000 5000 4000 3000
- Page 273 and 274:
Architecture (AMBA) a new bus archi
- Page 275 and 276:
In order to ensure the smooth proce
- Page 277 and 278:
ISBN 978-952-5726-09-1 (Print) Proc
- Page 279 and 280:
In this paper, we adopt two Sobel o
- Page 281 and 282:
ISBN 978-952-5726-09-1 (Print) Proc
- Page 283 and 284:
four layers.The far right of the gr
- Page 285 and 286:
ISBN 978-952-5726-09-1 (Print) Proc
- Page 287 and 288:
TABLE II. OPERATIONAL EMPLOYEE TABL
- Page 289 and 290:
A. Object-relational Type To audit
- Page 291 and 292:
to execution time. Also, DBA would
- Page 293 and 294:
Liping Chen .......................