Download - Academy Publisher
Download - Academy Publisher
Download - Academy Publisher
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
Step4 calculate the new subordinate-matrixU in each<br />
time window through formula<br />
k<br />
u = 1/ ∑ ( d / d )<br />
ij ij rl<br />
l=<br />
1<br />
2/( m−1)<br />
Step5 Loop computations step3 and step4 until the<br />
cluster rule function is less than a threshold<br />
value. The value is the cluster result. Cluster rule<br />
m 2<br />
function is J ( U, V) u d ( x , v )<br />
n<br />
m ij ij j i<br />
j= 1 i=<br />
1<br />
c<br />
= ∑∑ .<br />
Through the above calculation step the deviation of<br />
membership of every sample point could be determined<br />
in its time window. According to the rule of the<br />
maximum deviation of membership in fuzzy date set, it<br />
should be determined that which cluster center every<br />
sample point belongs to so as to make sure whether there<br />
are DDoS attacks in current network.<br />
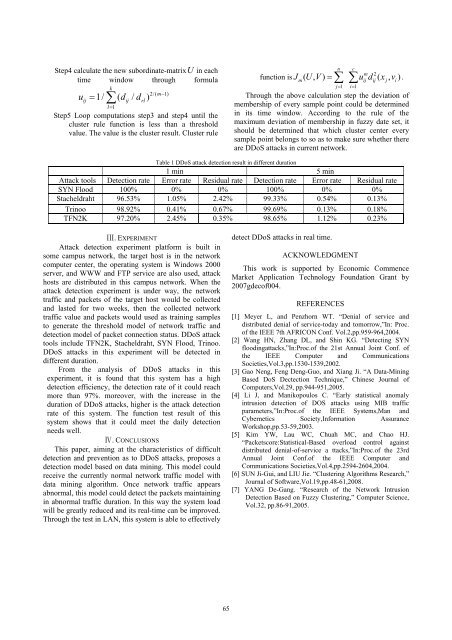
Table 1 DDoS attack detection result in different duration<br />
1 min 5 min<br />
Attack tools Detection rate Error rate Residual rate Detection rate Error rate Residual rate<br />
SYN Flood 100% 0% 0% 100% 0% 0%<br />
Stacheldraht 96.53% 1.05% 2.42% 99.33% 0.54% 0.13%<br />
Trinoo 98.92% 0.41% 0.67% 99.69% 0.13% 0.18%<br />
TFN2K 97.20% 2.45% 0.35% 98.65% 1.12% 0.23%<br />
Ⅲ. EXPERIMENT<br />
Attack detection experiment platform is built in<br />
some campus network, the target host is in the network<br />
computer center, the operating system is Windows 2000<br />
server, and WWW and FTP service are also used, attack<br />
hosts are distributed in this campus network. When the<br />
attack detection experiment is under way, the network<br />
traffic and packets of the target host would be collected<br />
and lasted for two weeks, then the collected network<br />
traffic value and packets would used as training samples<br />
to generate the threshold model of network traffic and<br />
detection model of packet connection status. DDoS attack<br />
tools include TFN2K, Stacheldraht, SYN Flood, Trinoo.<br />
DDoS attacks in this experiment will be detected in<br />
different duration.<br />
From the analysis of DDoS attacks in this<br />
experiment, it is found that this system has a high<br />
detection efficiency, the detection rate of it could reach<br />
more than 97%. moreover, with the increase in the<br />
duration of DDoS attacks, higher is the attack detection<br />
rate of this system. The function test result of this<br />
system shows that it could meet the daily detection<br />
needs well.<br />
Ⅳ. CONCLUSIONS<br />
This paper, aiming at the characteristics of difficult<br />
detection and prevention as to DDoS attacks, proposes a<br />
detection model based on data mining. This model could<br />
receive the currently normal network traffic model with<br />
data mining algorithm. Once network traffic appears<br />
abnormal, this model could detect the packets maintaining<br />
in abnormal traffic duration. In this way the system load<br />
will be greatly reduced and its real-time can be improved.<br />
Through the test in LAN, this system is able to effectively<br />
detect DDoS attacks in real time.<br />
ACKNOWLEDGMENT<br />
This work is supported by Economic Commence<br />
Market Application Technology Foundation Grant by<br />
2007gdecof004.<br />
REFERENCES<br />
[1] Meyer L, and Penzhorn WT. “Denial of service and<br />
distributed denial of service-today and tomorrow,”In: Proc.<br />
of the IEEE 7th AFRICON Conf. Vol.2,pp.959-964,2004.<br />
[2] Wang HN, Zhang DL, and Shin KG. “Detecting SYN<br />
floodingattacks,”In:Proc.of the 21st Annual Joint Conf. of<br />
the IEEE Computer and Communications<br />
Societies,Vol.3,pp.1530-1539,2002.<br />
[3] Gao Neng, Feng Deng-Guo, and Xiang Ji. “A Data-Mining<br />
Based DoS Dectection Technique,” Chinese Journal of<br />
Computers,Vol.29, pp.944-951,2005.<br />
[4] Li J, and Manikopoulos C. “Early statistical anomaly<br />
intrusion detection of DOS attacks using MIB traffic<br />
parameters,”In:Proc.of the IEEE Systems,Man and<br />
Cybernetics Society,Information Assurance<br />
Workshop,pp.53-59,2003.<br />
[5] Kim YW, Lau WC, Chuah MC, and Chao HJ.<br />
“Packetscore:Statistical-Based overload control against<br />
distributed denial-of-service a ttacks,”In:Proc.of the 23rd<br />
Annual Joint Conf.of the IEEE Computer and<br />
Communications Societies,Vol.4,pp.2594-2604,2004.<br />
[6] SUN Ji-Gui, and LIU Jie. “Clustering Algorithms Research,”<br />
Journal of Software,Vol.19,pp.48-61,2008.<br />
[7] YANG De-Gang. “Research of the Network Intrusion<br />
Detection Based on Fuzzy Clustering,” Computer Science,<br />
Vol.32, pp.86-91,2005.<br />
65