Download - Academy Publisher
Download - Academy Publisher
Download - Academy Publisher
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
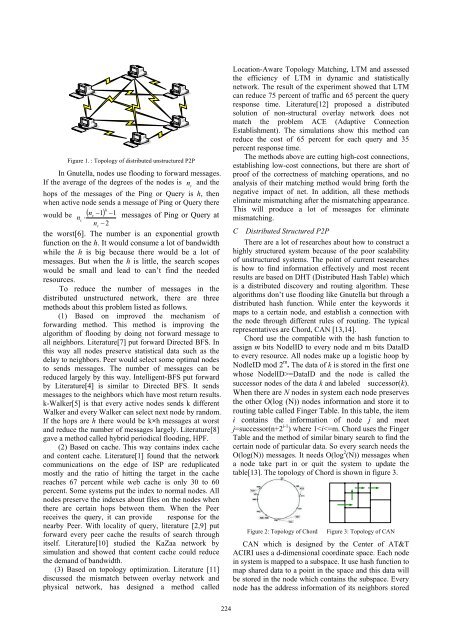
Figure 1. : Topology of distributed unstructured P2P<br />
In Gnutella, nodes use flooding to forward messages.<br />
If the average of the degrees of the nodes is n and the<br />
c<br />
hops of the messages of the Ping or Query is h, then<br />
when active node sends a message of Ping or Query there<br />
h<br />
would be ( nc<br />
−1)<br />
−1<br />
n ⋅ messages of Ping or Query at<br />
c<br />
nc<br />
−2<br />
the worst[6]. The number is an exponential growth<br />
function on the h. It would consume a lot of bandwidth<br />
while the h is big because there would be a lot of<br />
messages. But when the h is little, the search scopes<br />
would be small and lead to can’t find the needed<br />
resources.<br />
To reduce the number of messages in the<br />
distributed unstructured network, there are three<br />
methods about this problem listed as follows.<br />
(1) Based on improved the mechanism of<br />
forwarding method. This method is improving the<br />
algorithm of flooding by doing not forward message to<br />
all neighbors. Literature[7] put forward Directed BFS. In<br />
this way all nodes preserve statistical data such as the<br />
delay to neighbors. Peer would select some optimal nodes<br />
to sends messages. The number of messages can be<br />
reduced largely by this way. Intelligent-BFS put forward<br />
by Literature[4] is similar to Directed BFS. It sends<br />
messages to the neighbors which have most return results.<br />
k-Walker[5] is that every active nodes sends k different<br />
Walker and every Walker can select next node by random.<br />
If the hops are h there would be k×h messages at worst<br />
and reduce the number of messages largely. Literature[8]<br />
gave a method called hybrid periodical flooding, HPF.<br />
(2) Based on cache. This way contains index cache<br />
and content cache. Literature[1] found that the network<br />
communications on the edge of ISP are reduplicated<br />
mostly and the ratio of hitting the target in the cache<br />
reaches 67 percent while web cache is only 30 to 60<br />
percent. Some systems put the index to normal nodes. All<br />
nodes preserve the indexes about files on the nodes when<br />
there are certain hops between them. When the Peer<br />
receives the query, it can provide response for the<br />
nearby Peer. With locality of query, literature [2,9] put<br />
forward every peer cache the results of search through<br />
itself. Literature[10] studied the KaZaa network by<br />
simulation and showed that content cache could reduce<br />
the demand of bandwidth.<br />
(3) Based on topology optimization. Literature [11]<br />
discussed the mismatch between overlay network and<br />
physical network, has designed a method called<br />
Location-Aware Topology Matching, LTM and assessed<br />
the efficiency of LTM in dynamic and statistically<br />
network. The result of the experiment showed that LTM<br />
can reduce 75 percent of traffic and 65 percent the query<br />
response time. Literature[12] proposed a distributed<br />
solution of non-structural overlay network does not<br />
match the problem ACE (Adaptive Connection<br />
Establishment). The simulations show this method can<br />
reduce the cost of 65 percent for each query and 35<br />
percent response time.<br />
The methods above are cutting high-cost connections,<br />
establishing low-cost connections, but there are short of<br />
proof of the correctness of matching operations, and no<br />
analysis of their matching method would bring forth the<br />
negative impact of net. In addition, all these methods<br />
eliminate mismatching after the mismatching appearance.<br />
This will produce a lot of messages for eliminate<br />
mismatching.<br />
C Distributed Structured P2P<br />
There are a lot of researches about how to construct a<br />
highly structured system because of the poor scalability<br />
of unstructured systems. The point of current researches<br />
is how to find information effectively and most recent<br />
results are based on DHT (Distributed Hash Table) which<br />
is a distributed discovery and routing algorithm. These<br />
algorithms don’t use flooding like Gnutella but through a<br />
distributed hash function. While enter the keywords it<br />
maps to a certain node, and establish a connection with<br />
the node through different rules of routing. The typical<br />
representatives are Chord, CAN [13,14].<br />
Chord use the compatible with the hash function to<br />
assign m bits NodelID to every node and m bits DataID<br />
to every resource. All nodes make up a logistic hoop by<br />
NodleID mod 2 m . The data of k is stored in the first one<br />
whose NodelID>=DataID and the node is called the<br />
successor nodes of the data k and labeled successor(k).<br />
When there are N nodes in system each node preserves<br />
the other O(log (N)) nodes information and store it to<br />
routing table called Finger Table. In this table, the item<br />
i contains the information of node j and meet<br />
j=successor(n+2 i-1 ) where 1